The Active Directory Database
Networks are collections of users, computers, printers and resources. In pre-Windows 2000 domains information was scattered throughout the network, and finding an object would have needed several searches. Windows 2000 introduced the Active Directory Service. Active Directory is designed to store information about all of the objects on the network, including Users, Groups, Computers, Printers and even software.
Use the buttons below to navigate through the lesson
Using the Active Directory Service, network objects can be easily located. The task of searching for the account department’s colour printer, for example, is made a lot easier. Using Active Directory, every object on the network can be controlled. Active Directory offers tighter security and easier administration. Everything on the network can be managed from one location. Active Directory groups everything on the network into a domain. Group policies can be applied to control what users can and can’t do as well as what applications are to be installed on workstations.
Microsoft’s Active directory is based on the X500 Directory Standard. The X500 standard is also used by other directory services such as Novell Directory Services. The X500 standard states that a directory service should use the DAP (Directory Access Protocol) for accessing information in the directory. Active Directory uses an implementation of the DAP Protocol known as LDAP (Lightweight Directory Access Protocol). Because of these standards Microsoft’s Active Directory can easily interoperate with other X500 Based directory services.
Windows Server 2008 continues to support Active Directory adding many new features to the Windows 2000 implementation. As well as enhanced management tools, Windows Server 2008 adds support for cross-forest transitive trusts (explained later), Domain rename, Domain Controller rename and Application Directory Partitions. Windows Server 2008 Domains remain compatible with Windows 2000 Domains. However when used with the latter not all of the new features are available.
Active Directory Objects
Everything in the Active Directory Database is an object. These objects can be users, groups, computers, printers and even security policies. An entire Active Directory domain is itself classed as an Active Directory object. Most Active Directory objects can be controlled using group policies, allowing the administrator greater control over the network.
Active Directory Domains
An Active Directory domain is a collection of objects grouped together into a secure environment. The Domain is controlled by a Domain Controller. The Domain Controller stores the Active Directory database. The Domain Controller controls what the members of the domain can and can’t do. Using the Active Directory, clients on the domain can easily locate one another and find any resources such as shared folders & printers easily. In this configuration all security policies are managed centrally, i.e. The Domain Controller decides what all the client machines can and can’t do, allowing for a more secure and easily managed environment.
In a domain, all security is managed centrally. Fred’s details are stored on the Domain Controller. The domain controller feeds Fred’s details into any workstation onto which he logs. In a domain, all security is managed centrally. Fred’s details are stored on the Domain Controller. The domain controller feeds Fred’s details into any workstation onto which he logs. Fred can log onto any computer in the domain and his profile will follow him, e.g. His desktop wallpaper and My Documents folder will be the same on all the machines in the domain.
In an Active Directory environment domains can be grouped into trees. Here, three different domains all share a common namespace, i.e. they all end in “es-net.co.uk”.
Each domain has a separate Domain Controller and is essentially treated as a separate domain. They are however linked and resources can easily be shared between domains. In order to create an Active Directory tree, a root domain is needed. The other domains are joined to the tree when they are created and they become child domains. Trees can be further grouped into forests. These two different trees have a separate namespace, but users can easily share and locate resources. The different domain trees in a forest act completely independently of each another. In order to create a forest, a root domain must exist. An existing domain tree cannot be joined to another tree without first destroying the tree and recreating it. Forests cannot be further grouped.
Active Directory Forests are commonly used for joining two separate companies into one Active Directory Environment whilst keeping separate identities. However as mentioned previously, two forests cannot be joined into a single forest without first destroying one of the forests and recreating it in the other. There are workarounds for this such as cross-forest transitive trusts which you will read about later.
Active Directory Schema
Domain Controllers in a forest store information only for their own domains, but they share and replicate information such as trust, site and services information. For this reason all domains in an Active Directory tree/forest share a common schema.
The Schema states the format of information stored in the Active Directory database. For example, the User object in Active Directory has several properties such as username, password, phone number, etc. The schema can be modified to include additional properties.
Applications such as Exchange and SQL Server modify the schema automatically. For example, Exchange adds a mail property to the user account. The Active Directory schema must be consistent for the entire Active Directory forest. It is The Schema Master’s role to ensure that the schema is consistent across the forest. Replication will not take place until the schema is consistent . I.E all domains have Exchange installed.
Active Directory Replication Overview
A Windows 2008 Domain can contain more than one Domain Controller. All Domain Controllers in the domain will store the Active Directory database. Microsoft recommends that you always have more than one Domain Controller running a domain. Having additional Domain Controllers allows for fault-tolerance and load-balancing. This domain has two controllers. Any changes made on either Domain Controller will be replicated to the other. There are no primary or secondary Domain Controllers as in NT 4.0. All Domain Controllers in a Windows 2000/2003/2008 Domain are equal. This is known as a multi-master arrangement.
In an Active Directory Forest or Tree, each domain controller stores a copy of its own domain. However, all domain controllers inside a forest/tree replicate common information such as the schema and services information.
Although only Domain Controllers within a forest can replicate , Domains in different forests can share resources and authenticate users by using trusts. All Domains within an Active Directory forest trust each other by default, however trusts can be setup manually between Domains in different forests. All Domains within a forest have transitive trusts which basically says that if Domain A trusts Domain B and Domain B trusts Domain C then Domain A will also trust Domain C.
Windows NT 4.0 Trusts
Windows NT 4.0 Domains could not use transitive trusts therefore a trust had to be setup between every single domain within an organization.
Windows 2000 Trusts
Within large organizations trusts became extremely difficult to manage. However because of the transitive nature of Windows 2000 trusts, trusts became easier to manage. Only 3 trusts are now needed because all of the trusts are transitive. Because Domain A trusts Domain C, and Domain D trusts Domain B which in turn trusts A, Domain D also trusts Domain C.
Active Directory Trusts
The downside to Windows 2000 trusts was that trusts between Domains in separate forests are not transitive. Therefore in the above configuration every domain would need to be configured. Windows Server 2003/2008 Domains now support cross forest transitive trusts. This allows every domain in one forest to trust every domain in another by simply creating a forest trust. However the trust is only transitive between two forests. Only two forests are allowed because if all trusts were transitive, then if company A’s network had a trust with Company B’s network and Company B’s network had a trust with Company C’s network (who had no business with Company A) then users in company C’s network could access resources in company A’s.
Domain and Forest Functional Levels
Active Directory can function in different modes, these modes allow a varying degree of compatibility with older versions of Windows. The downside to using older Domain Controllers on your domain is that not all of the new features of Windows Server 2008 can be used. Since most installations of Windows Server 2008 will be upgrades, Domain and Forest modes allow your domain to continue to interoperate until all machines have been upgraded.
Domain Functional Levels
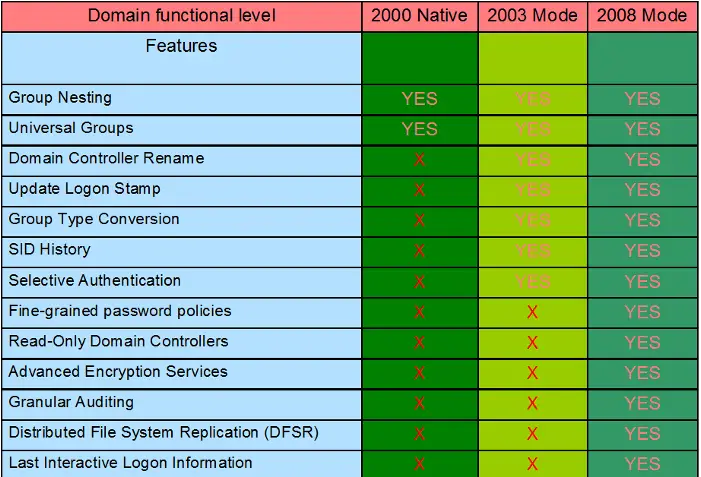
Within a Windows Server 2008 forest each domain can be given a domain functional level. The functional level determines which Windows Domain Controllers can exist on the domain. The Domain Functional level at which a domain is configured effects every domain controller in that domain. The different domain functional levels allow varying degrees of compatibility whilst compromising various features. The following lists the various domain functional levels available.
Windows 2000 Native Mode
Windows 2000 Native Mode domains allow only Windows 2000/2003/2008 Domain Controllers. Although Windows 2000 Native Mode domains provide the flexibility to have both Windows 2000 and Windows 2003 domain controllers within a domain, many of the new features of Windows 2008 domains still cannot be used. Universal groups and group nesting are available, however you cannot rename a Domain Controller or use some of the other new features of Windows Server 2008 domains.
Windows Server 2003 Mode
Windows Server 2003 domains allow only Windows Server 2003/2008 Domain Controllers. Features and benefits include all default Active Directory features, all features from the Windows 2000 native domain functional level, plus:
- Domain Controller Rename
- Update Logon Stamp
- Universal Groups
- Group Nesting
- Group Type Conversion
- SID History
- Selective Authentication
Windows Server 2008 Mode
Windows Server 2008 domains allow only Windows Server 2008 Domain Controllers. Features and benefits include all default Active Directory features, all features from the Windows 2003 domain functional level, plus:
- Fine-grained password policies
- Read-Only Domain Controllers
- Advanced Encryption Services
- Granular Auditing
- Distributed File System Replication (DFSR)
- Last Interactive Logon Information